Humans tend to move on to the next big thing quickly, and with rapidly changing security and regulatory environments, CISOs are no different. We all face new challenges daily, but as we focus on the latest priority in front of us, we must also remember to look back and revisit previous events to ensure we’re practicing hard lessons learned.
Humans tend to move on to the next big thing quickly, and with rapidly changing security and regulatory environments, CISOs are no different. We all face new challenges daily, but as we focus on the latest priority in front of us, we must also remember to look back and revisit previous events to ensure we’re practicing hard lessons learned.
Thousands of hacks and data breaches have been reported this year, with victims ranging from public and private companies to local governments and school districts. However, several breaches stand out to me, and now that the dust has settled on them, I think they warrant a deeper dive to uncover what lessons can be gleaned from them.
In this post, I’ll share the story of three data breaches and highlight the salient details you need to know to protect your organization in this age of cybercrime.
Three Significant Data Breaches in 2022
- The Okta Breach
Okta works with several partners to help manage its enterprise. Hackers targeted an employee of one of these partners, the Sitel Group, who had privileged access to provide customer service to Okta clients and data. That account was empowered to reset passwords and reset multifactor authentication.
The Sitel Group serves many more customers than Okta. To perform their jobs, support staff often need administrative privileges in their customer’s environment. The attack highlights the increased risk of outsourcing access to your organization’s internal environment.
- The Microsoft Breach
In March, Microsoft revealed that an employee account was compromised, which granted hackers “limited access” to Microsoft’s systems and allowed the theft of the company’s source code. Microsoft referenced the hackers’ use of “social engineering and identity-centric tactics” in a blog post detailing the breach. This attack illustrates why training employees about phishing and other social engineering tactics is so important.
- The Nvidia Breach
Nvidia, one of the world’s largest graphics processing unit (GPU) manufacturers, was breached in a cyberattack that resulted in the theft and release of over a terabyte of proprietary data and over 71,000 employee credentials. In a statement after the breach, an Nvidia spokesperson did not disclose how hackers were able to gain access, only referring to the attack as a “cybersecurity incident,” but a well-known hacking group quickly took credit for the attack.
What Do These Attacks Have in Common?
It is no coincidence that I am looking back at these three cyber events. The hacks were all claimed by a hacking group known as the Lapsus$ group. Lapsus$ claimed responsibility for the Okta breach, the Microsoft breach, and the breach of Nvidia, among other high-profile targets. The most surprising piece of information about that group is it’s allegedly run by a group of teenagers.
Lessons to be Learned from Teenagers?
The tactics used by the Lapsus$ group are wholly unsophisticated but have still proven time and time again to be effective. The good news is that because their tactics are easily thwarted, organizations have plenty of opportunities to avoid getting hacked by following best practices.
- Lesson #1: Lapsus$ primarily relied on social engineering schemes to gain access to a target directly or seek access via an organization’s supply chain or service providers. The group claimed that its goal was financial and that it had no political agenda; however, its chaotic approach caused just as destruction in its pursuit of exploiting data.
- Lesson #2: The Lapsus$ group’s attacks should be a reminder that even the most robust cyber defenses can be circumvented if attackers exploit weak links in the chain. These weak links can be found in both the technical and human domains, but the likeliest way for hackers to gain access is via end-users. As a result, organizations need to be vigilant in educating employees about cyber threats and how to identify and avoid them.
- Lesson #3: Third-party risk management is also critical in protecting against the type of supply chain attack used against Okta. Companies need to vet their service providers and have security protocols in place to prevent attackers from exploiting these relationships to gain access to sensitive data.
Related Content → What’s a Supply Chain Attack? Watch the video to learn more.
- Lesson #4: Additionally, the Lapsus$ group’s attacks show that even small groups of relatively primitive attackers can cause much damage. This fact should be a reminder that organizations must be prepared for all threats, not just those from well-funded and well-developed cybercriminals.
It is important to remember that breaches can and will happen, whether perpetrated by Lapsus$ or other sources, and your company’s response can make all the difference in whether it will survive unscathed. The risk of lost revenue, fines and penalties, and reputational damage require that your company set and follow disaster response and recovery plans.
Reduce Your Risk from Data Breaches?
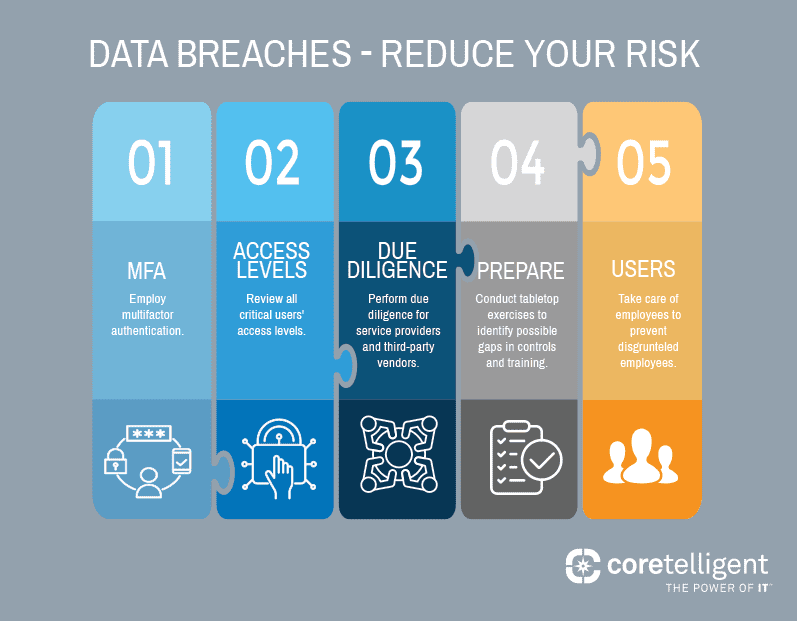
There are a variety of actions your firm can take to reduce your risk of being hacked, but here are a few key points to keep in mind:
- Employ multifactor authentication.
- Review all critical users’ access levels.
- Perform due diligence for service providers and third-party vendors.
- Conduct tabletop exercises to identify possible gaps in controls and training. For example, if an internal employee shared their credentials with an attacker, how could you tell?
- Take care of your employees. Disgruntled employees are more susceptible to bribes.
Related Content → Evaluate your security readiness with our Cybersecurity Checklist.
Next Steps
Lapsus$’s attacks are a reminder that cyber defenses can be circumvented if attackers can exploit the weakest links in the chain. The best defense is to employ a multilayered cybersecurity solution that includes end-user training, comprehensive security policies and protocols, incident response planning, regular security audits, and more.
In today’s digital world, data is the new currency. And like any other type of currency, it needs to be protected from those who would exploit it. Unfortunately, the Lapsus$ group is just one example of the many cyber criminals out there looking to profit from the data of others.
Whether you work with an internal team or outsource your IT functions, employing robust cybersecurity solutions and regularly reviewing them against your risk profile is critical. Reach out to our security professionals for help evaluating your cybersecurity program to find gaps and areas that need improvement. Implementing security controls is not “set it and forget it” but must routinely be assessed to match the needs of your business and the external challenges of today’s cyber landscape.
 About Jason
About Jason
Jason Martino is passionate about the intersection of security and compliance. He is responsible for Coretelligent’s internal cybersecurity programs, governance, risk, compliance activities, and educating staff and customers on an ever-evolving threat landscape.